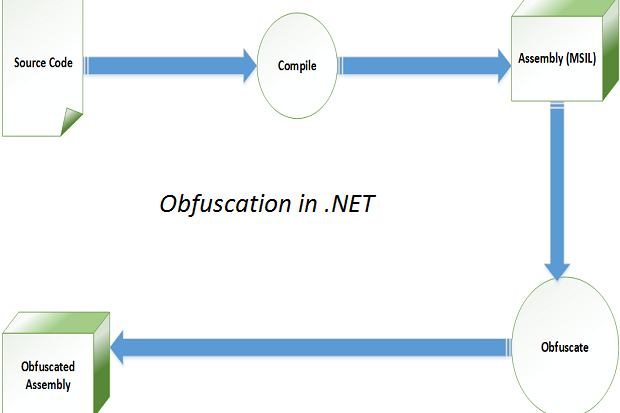
Obfuscation Techniques Ppt Powerpoint Presentation Styles Ideas Cpb | Presentation Graphics | Presentation PowerPoint Example | Slide Templates
GitHub - Dgeeth9595/Android-Obfuscation-Tools: Android Obfuscation tools that work at dalvik bytecode level.





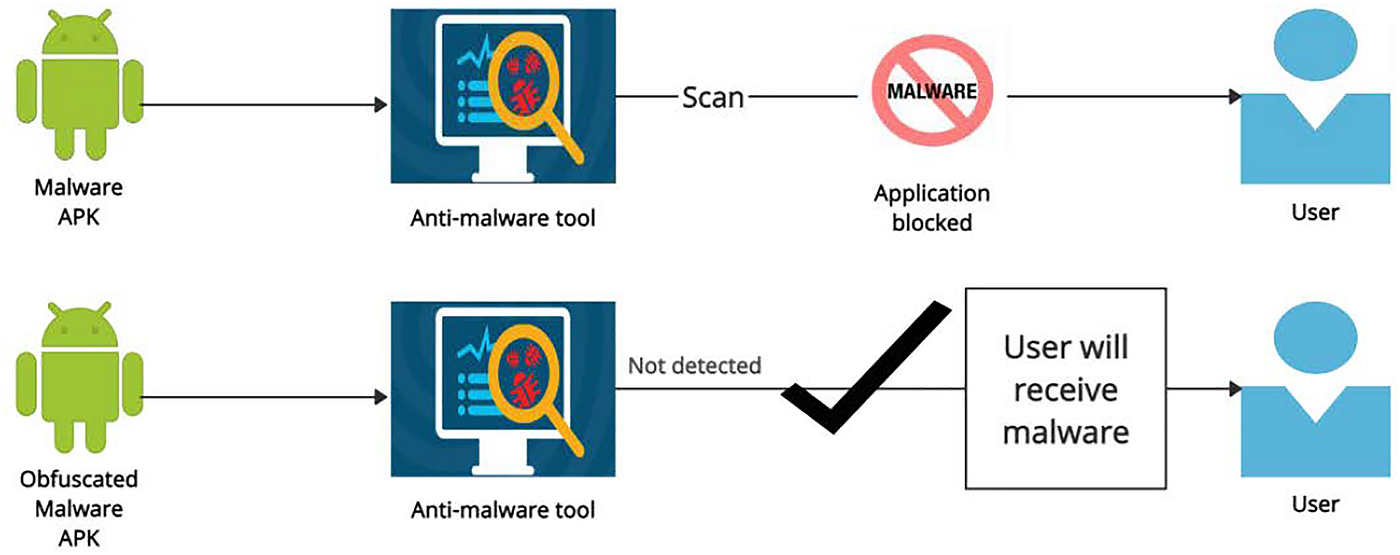
![On the evaluation of android malware detectors against code-obfuscation techniques [PeerJ] On the evaluation of android malware detectors against code-obfuscation techniques [PeerJ]](https://dfzljdn9uc3pi.cloudfront.net/2022/cs-1002/1/fig-3-full.png)